Telegram declined to fix a scenario in which the flaw can be exploited, spurring a Trustwave researcher to decline a bug bounty and to disclose his findings instead.
A vulnerability in a high-level privacy feature of Telegram on macOS that sets up a “self-destruct” timer for messages on both the sender’s and recipient’s devices can allow someone to retrieve these messages even after they’ve been deleted, a researcher has found.
Reegun Richard Jayapaul, Trustwave SpiderLabs Lead Threat Architect, discovered the flaw in the Self-Destruct feature of Telegram MacOS, which is part of the Secret-Chats aspect of the messaging app that uses end-to-end encryption.
This encryption – the key to which even Telegram administrators do not have – “is meant for people who are concerned about the security and privacy of their chat history,” he said in a blog post about his findings published Thursday.
Indeed, Telegram in general is widely viewed as one of the more secure messaging apps; many users have opted to switch from Facebook’s WhatsApp to Telegram because they are concerned about their privacy.
Jayapaul worked with Telegram to patch the flaw, which can allow the privacy of users to be violated via two scenarios. In doing so, he said he learned of a caveat of the company’s vulnerability disclosure program that prevents researchers from disclosing a flaw if they agree to accept a bug bounty – something Jayapaul said he was not on board with.
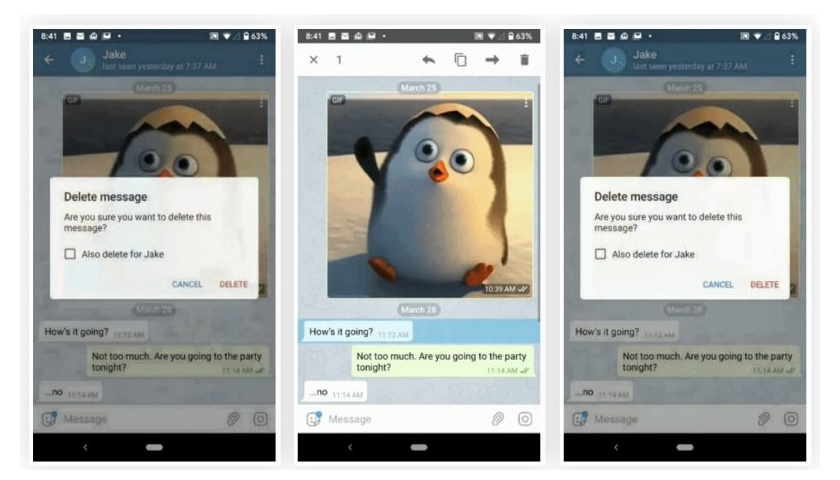
In the first scenario, Shared Location, video and audio messages can leak even after the messages have been timed to self-destruct on both the sender’s and recipient’s device, he wrote. In the second scenario, these same messages can leak without a recipient even opening or deleting the message.
However, while Telegram fixed the issue creating the first scenario, the company declined to fix the second. Because of this, the Trustwave researcher declined the bug bounty from Telegram, as it “would have kept us from disclosing this research to the community,” Jayapaul wrote.
“We feel bug bounties that require permanent silence about a vulnerability do not help the broader community to improve their security practices and can serve to raise questions about what exactly the bug bounty is compensating the individual for – reporting a vulnerability to the bounty payer or their silence to the broader community,” he said. “This is especially serious in this case, where one of the issues reported went unaddressed.”
Read more here: threatpost.com